EthicalHackers
Pentester et hacker indépendant pour les sociétés
Category Archives: Exploitation
A phantom has been haunting me: a deep dive into SMBGhost (part 1)
What is SMBGhost SMBGhost (CVE-2020-0796) is a vulnerability affecting SMB 3.1, and more precisely one of its decompression function. As SMB 3.1 added support for data compression in order to save bandwidth, it added a decompression function presenting an integer overflow resulting in multiple subsequent buffer overflows. Those buffer overflows are exploitable in a way…
Ressource Based Constrained Delegation abuse through GenericWrite
Someone asked me recently what an attacker could do if he had full acess to a computer object in an active directory environment. While i knew from memory it was possible to leverage this into a full compromise through RBCD abuse, I never had to implement the attack in an engagement. Knowing being half the…
One IPv6 packet to compromise your whole infrastructure
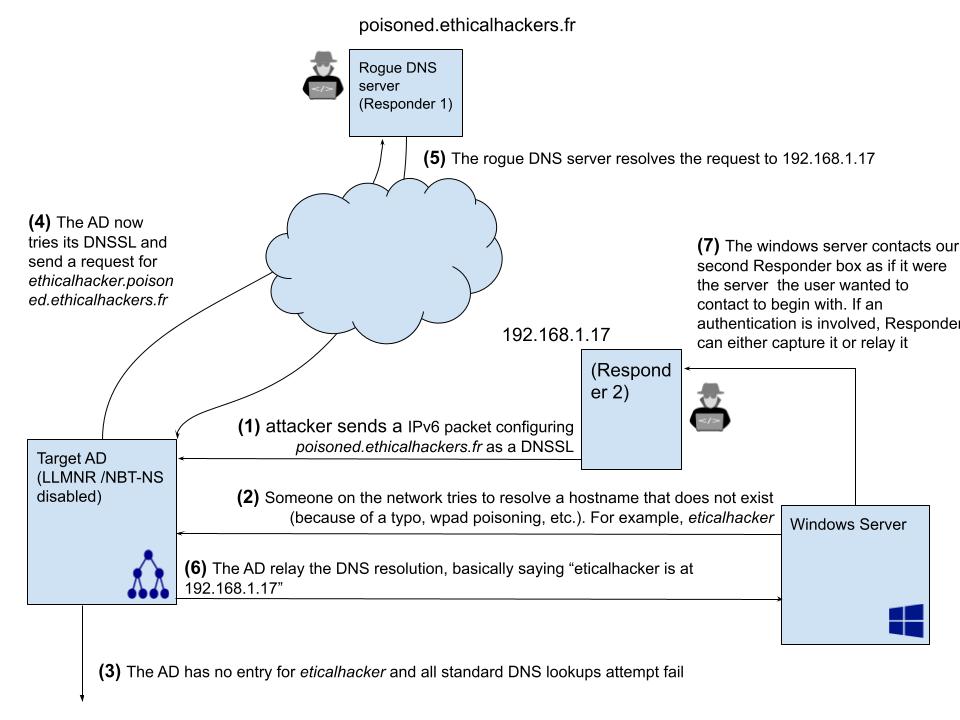
One IPv6 packet to compromise your whole infrastructure While doing my morning “I check new stuff on twitter” routine, I read one tweet from Laurent Gaffié (author of Responder, RunFinger.py, etc.) talking about DNS poisoining through IPv6 that I found so simple that I had a hard time believing it was really that easy. He actually describes the…
How to be a good pentester: have a scalable and maintainable practice environment (Part 2)
How to be a good pentester: have a scalable and maintainable practice environment (Part 2) In the “How to be a good pentester” series, I share my thoughts on what makes a pentester good, and what I do to try to be one. In this particular entry, we’ll delve into making a dummy AD environment …
How to be a good pentester: have a scalable and maintainable practice environment (Part 1)
In the “How to be a good pentester” series, I share my thoughts on what makes a pentester good, and what I do to try to be one. In this particular entry, we’ll delve into making a dummy Active Directory environment with servers and workstations through Vagrant, workstation, and Ansible. Part 1 will be about…
A flink to the past : Heap overflow through unsafe unlinking

Prepare everything I had a lot of problem finding the needed tools for XP SP1, because it is just so old. First of all, I couldn’t find a ” Visual 2008 Express C++ Edition ” executable compatible with XP SP1. I also couldn’t find symbols for XP SP1. What I ended up doing is installing…
A flink to the past : introduction

What we will explain here is how to obtain a basic 4 bytes write primitive through a heap overflow in… Windows XP SP1.
To do so, I’ll follow this mr_me tutorial, which explains how to abuse the way the heap unlinks memory chunks before XP SP2, and try to expand on anything that I had a hard time grasping.
Keep in mind that my knowledge on heap management was non-existent before starting to write this, so if you see anything that doesn’t seem right, do not hesitate to leave a comment.
